VMware : VCSA ERROR certificate-manager ‘lstool get’ failed: 1
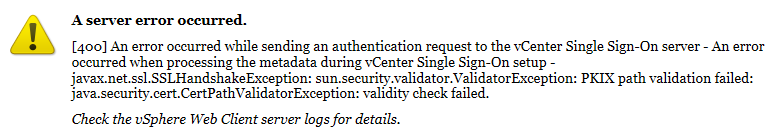
If you are using vCenter, you are were maybe looking to replace the default self-signed certificate with an enterprise signed-certificate for security reasons. The biggest challenge is not to forget the expiration date otherwise access to the vCenter will be blocked with errors as per below:
The process of replacing a certificate has been simplified since 6.0 version: indeed the certificate manager script takes care of everything.
However, this time I faced an error when replacing the certificate with a message operation failed and rollback also failed.
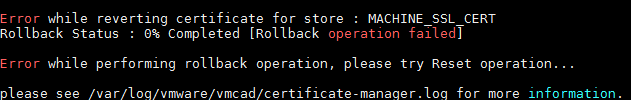
As recommended, I checked the certificate-manager.log on /var/log/vmware/certificate-manager and found the following line: ’lstool get’ failed:1
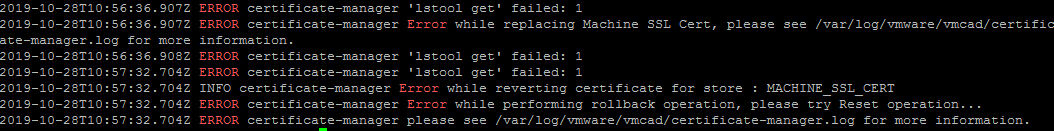
I have no idea what this means so googled it and find the VMware KB 2150057.
So, it seems this issue occurs when there are third-party extensions with no valid certificates registered to vCenter Server.
To resolve it, we need to remove the third party extension through the Managed Object Browser and retry replacing the certificates. But, since the certificate is no more valid we cannot log to the MOB interface anymore..
The workaround given by vmware support is to modify the script certificateManagerHelper.py that can be found /usr/lib/vmware/site-packages/cis searching for the following block:

Edit the block by commenting “#raise Exception(“‘lstool get’ failed: %d” % rc)” and add rc = 0;
The modification will force the certificate manager script to set the return code to zero and proceed with certificate change. After that change, I was able to successfully update the SSL certificates without any issue!
Don’t forget before any operation to take snapshot backup your VCSA